156-215.81 Exam
How Many Questions Of 156-215.81 Dump

Master the 156-215.81 Check Point Certified Security Administrator R81 content and be ready for exam day success quickly with this Ucertify 156-215.81 actual test. We guarantee it!We make it a reality and give you real 156-215.81 questions in our CheckPoint 156-215.81 braindumps.Latest 100% VALID CheckPoint 156-215.81 Exam Questions Dumps at below page. You can use our CheckPoint 156-215.81 braindumps and pass your exam.
Also have 156-215.81 free dumps questions for you:
NEW QUESTION 1
Which firewall daemon is responsible for the FW CLI commands?
- A. fwd
- B. fwm
- C. cpm
- D. cpd
Answer: A
NEW QUESTION 2
You can see the following graphic: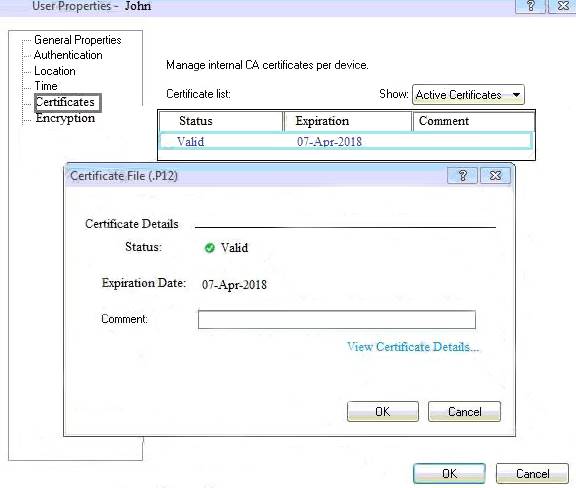
What is presented on it?
- A. Properties of personal .p12 certificate file issued for user John.
- B. Shared secret properties of John’s password.
- C. VPN certificate properties of the John’s gateway.
- D. Expired .p12 certificate properties for user John.
Answer: A
NEW QUESTION 3
When doing a Stand-Alone Installation, you would install the Security Management Server with which other Check Point architecture component?
- A. None, Security Management Server would be installed by itself.
- B. SmartConsole
- C. SecureClient
- D. SmartEvent
Answer: D
NEW QUESTION 4
An administrator wishes to enable Identity Awareness on the Check Point firewalls. However they allow users to use company issued or personal laptops. Since the administrator cannot manage the personal laptops, which of the following methods would BEST suit this company?
- A. AD Query
- B. Browser-Based Authentication
- C. Identity Agents
- D. Terminal Servers Agent
Answer: B
NEW QUESTION 5
Which two of these Check Point Protocols are used by ?
- A. ELA and CPD
- B. FWD and LEA
- C. FWD and CPLOG
- D. ELA and CPLOG
Answer: B
NEW QUESTION 6
Which default Gaia user has full read/write access?
- A. admin
- B. superuser
- C. monitor
- D. altuser
Answer: A
Explanation:
Has full read/write capabilities for all Gaia features, from the Gaia Portal and the Gaia Clish. This user has a User ID of 0, and therefore has all of the privileges of a root user. monitor Has read-only capabilities for all features in the Gaia Portal and the Gaia Clish, and can change its own password. You must give a password for this user before the account can be used.
NEW QUESTION 7
Which Threat Prevention profile uses sanitization technology?
- A. Cloud/data Center
- B. perimeter
- C. Sandbox
- D. Guest Network
Answer: B
Explanation:
Strict Security for Perimeter Profile & Perimeter Profile use sanitization as a technology in Threat prevention profile
NEW QUESTION 8
Which of the following is the most secure means of authentication?
- A. Password
- B. Certificate
- C. Token
- D. Pre-shared secret
Answer: B
NEW QUESTION 9
What is UserCheck?
- A. Messaging tool user to verify a user’s credentials
- B. Communication tool used to inform a user about a website or application they are trying to access
- C. Administrator tool used to monitor users on their network
- D. Communication tool used to notify an administrator when a new user is created
Answer: B
Explanation:
https://sc1.checkpoint.com/documents/R81/WebAdminGuides/EN/CP_R81_NextGenSecurityGateway_Guide/T
NEW QUESTION 10
When using Monitored circuit VRRP, what is a priority delta?
- A. When an interface fails the priority changes to the priority delta
- B. When an interface fails the delta claims the priority
- C. When an interface fails the priority delta is subtracted from the priority
- D. When an interface fails the priority delta decides if the other interfaces takes over
Answer: C
NEW QUESTION 11
When configuring Anti-Spoofing, which tracking options can an Administrator select?
- A. Log, Alert, None
- B. Log, Allow Packets, Email
- C. Drop Packet, Alert, None
- D. Log, Send SNMP Trap, Email
Answer: A
Explanation:
Configure Spoof Tracking - select the tracking action that is done when spoofed packets are detected: Log - Create a log entry (default)
Alert - Show an alert None - Do not log or alert
https://sc1.checkpoint.com/documents/R81/WebAdminGuides/EN/CP_R81_SecurityManagement_AdminGuide
NEW QUESTION 12
When configuring Spoof Tracking, which tracking actions can an administrator select to be done when spoofed packets are detected?
- A. Log, send snmp trap, email
- B. Drop packet, alert, none
- C. Log, alert, none
- D. Log, allow packets, email
Answer: C
Explanation:
Configure Spoof Tracking - select the tracking action that is done when spoofed packets are detected:
NEW QUESTION 13
Which tool provides a list of trusted files to the administrator so they can specify to the Threat Prevention blade that these files do not need to be scanned or analyzed?
- A. ThreatWiki
- B. Whitelist Files
- C. AppWiki
- D. IPS Protections
Answer: A
NEW QUESTION 14
What is the SOLR database for?
- A. Used for full text search and enables powerful matching capabilities
- B. Writes data to the database and full text search
- C. Serves GUI responsible to transfer request to the DLE server
- D. Enables powerful matching capabilities and writes data to the database
Answer: A
NEW QUESTION 15
What SmartEvent component creates events?
- A. Consolidation Policy
- B. Correlation Unit
- C. SmartEvent Policy
- D. SmartEvent GUI
Answer: B
NEW QUESTION 16
To increase security, the administrator has modified the Core protection ‘Host Port Scan’ from ‘Medium’ to ‘High’ Predefined Sensitivity. Which Policy should the administrator install after Publishing the changes?
- A. The Access Control and Threat Prevention Policies.
- B. The Access Control Policy.
- C. The Access Control & HTTPS Inspection Policy.
- D. The Threat Prevention Policy.
Answer: D
Explanation:
https://supportcenter.checkpoint.com/supportcenter/portal?action=portlets.SearchResultMainAction&eventSubm
NEW QUESTION 17
Can multiple administrators connect to a Security Management Server at the same time?
- A. No, only one can be connected
- B. Yes, all administrators can modify a network object at the same time
- C. Yes, every administrator has their own username, and works in a session that is independent of other administrators
- D. Yes, but only one has the right to write
Answer: C
NEW QUESTION 18
To provide updated malicious data signatures to all Threat Prevention blades, the Threat Prevention gateway does what with the data?
- A. Cache the data to speed up its own function.
- B. Share the data to the ThreatCloud for use by other Threat Prevention blades.
- C. Log the traffic for Administrator viewing.
- D. Delete the data to ensure an analysis of the data is done each time.
Answer: B
Explanation:
Data from malicious attacks are shared between the Threat Prevention Software Blades and help to keep your network safe. For example, the signatures from threats that Threat Emulation identifies are added to the ThreatCloud for use by the other Threat Prevention blades. src
https://infosec.co.il/wp-content/uploads/2020/06/12-GAiA-R80.40-Threat-Prevention.pdf page 28.
NEW QUESTION 19
......
P.S. Easily pass 156-215.81 Exam with 340 Q&As 2passeasy Dumps & pdf Version, Welcome to Download the Newest 2passeasy 156-215.81 Dumps: https://www.2passeasy.com/dumps/156-215.81/ (340 New Questions)
